|
Fujitsu Strengthens Cyber-Security with AI Technology to Protect Against Deception Attacks
KAWASAKI, Japan, Oct 29, 2020 - (JCN Newswire) - Fujitsu Laboratories Ltd. today announced the development of a technology to make AI models more robust against deception attacks. The technology protects against attempts to use forged attack data to trick AI models into making a deliberate misjudgment when AI is used for sequential data consisting of multiple elements.
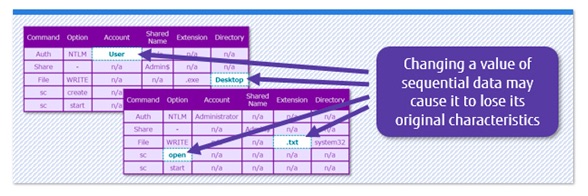 | | Figure 1: simple process of generating simulated data attack |
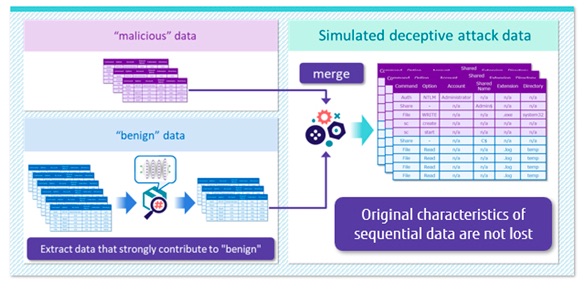 | | Figure 2: image of automatic generation of simulated attack data |
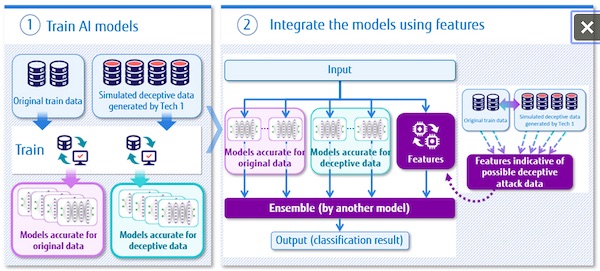 | | Figure 3 image of ensemble adversarial training techniques |
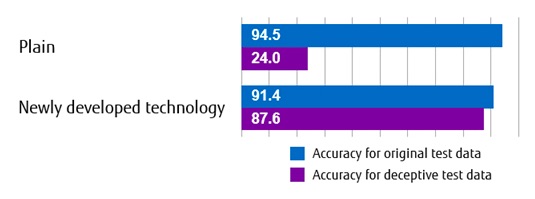 | | Figure 4: evaluation of the newly developed technology |
With the use of AI technologies progressing in various fields in recent years, the risk of attacks that intentionally interfere with AI's ability to make correct judgments represents a source of growing concern. Many suitable conventional security resistance enhancement technologies exist for media data like images and sound. Their application to sequential data such as communication logs and service usage history remains insufficient, however, because of the challenges posed by preparing simulated attack data and the loss of accuracy.
To overcome these challenges, Fujitsu has developed a robustness enhancement technology for AI models applicable to sequential data. This technology automatically generates a large amount of data simulating an attack and combines it with the original training data set to improve resistance to potential deception attacks while maintaining the accuracy of judgment.
By applying this technology to an AI model(1) developed by Fujitsu to judge the necessity of countermeasures against cyber-attacks, it was confirmed that misjudgment of about 88% can be prevented in our own attack test data.
Details of this technology will be announced at the Computer Security Symposium 2020 held from October 26 (Monday) to October 29 (Thursday).
Background
In recent years, AI has been increasingly used to analyze a vast range of data in fields as varied as medicine, social infrastructure, and agriculture. Nevertheless, the existence of security threats peculiar to AI represents a growing threat. Examples include attaching small stickers to road signs to confuse recognition systems and intentionally trying to trick AI models with slightly changed attack data in order to prevent a correct judgment. To help avoid these types of threats, an adversarial training technique has emerged in which simulated attack data created in advance is added to training data so that the AI model is not fooled when it encounters malicious actors.
Previous technologies remain insufficient for dealing with the challenges posed by sequential data, however. AI has a wide range of applications for this type of data, including for the detection of cyber-attacks and credit card fraud, and so a growing need exists to develop technologies that can be applied to sequential data to strengthen resistance against deception attacks.
Issues
One way that cyber-attacks can be detected is through the analysis of communication log data. For instance, when an attacker logs in from the first terminal to another terminal, executes written malware and performs a series of attack operations to spread infection, an AI model can detect the attack from the communication log of such operations. However, attackers disguise attacks by mixing them between legitimate administrative operations, such as collecting server logs or applying patches, which can lead to false negatives in the AI detection model.
In order to apply the adversarial training techniques to such a series of data, it is necessary to automatically generate a large amount of data simulating a deception attack as training data. In the case of media data such as images, it is possible to generate simulated attack data easily without damaging the characteristics of the original data by processing the data in units of pixels that cannot be discriminated by humans. However, in the case of sequential data, it is not clear which element affects the characteristics of the original data, so if you simply process a part of the data, the characteristics of the original data may be lost. (Figure 1) For example, the communication log data used to detect a cyber-attack is a series of log lines consisting of various elements such as the source of communication, the destination of the communication, the account used, the execution command, and the command arguments. In addition, even if simulated attack data can be generated, when it's used to train AI, it is necessary to be careful not to decrease the judgment accuracy for the original attack data.
Newly Developed Technology
Fujitsu has developed a technology that can automatically generate simulated attack data for training, which can be applied to AI models that analyze sequential data and enable training with less deterioration in the accuracy of attack detection. The features of the developed technology are as follows:
1. Automatic generation of simulated attack data
When creating simulated attack data, we first prepare the original attack data as a base and the data used for impersonation. In the case of cyber-attacks, the attacker wants to disguise malicious operations as benign operations, so the base data is the communication log data of the malicious operation, and the data used for the disguise is the communication log data of the benign operation. Next, the communication log data of benign operations used for the impersonation is analyzed by the AI model before the countermeasure, and the data with the impersonation effect which is easy to be judged as the benign operation is extracted referring to the result. This extracted data is combined with the communication log data of the base malicious operation, and it is generated as simulated attack data. Since the communication log data of the base malicious operation remains unchanged, a large amount of simulated attack data can be generated automatically without losing its original characteristics (Figure 2).
2. Ensemble adversarial training techniques
Using the original learning data set and the simulated attack data set generated with the new technique described above, two kinds of AI models are constructed: an AI model which works accurately for the original learning data and an AI model which works accurately for deception attack data (Figure 3) and the decision results of the two AI models are integrated by ensemble learning(2) using features indicative of possible deception attack data. In the case a cyber-attack is detected, it becomes possible to use ensemble learning to automatically and appropriately train AI models to decide which AI model's decision should be strongly reflected, since the number of log rows of communication log data and the number of duplicate log rows are used as indicative features. As a result, this technique increases the robustness to deception attacks while keeping loss of accuracy in the original data under control.
Effect
By using the newly developed technology, it is possible to strengthen the resistance of the AI model against deception attacks against sequential data. To demonstrate its effectiveness, Fujitsu applied the newly developed techniques to an AI model that determines the necessity of responding to cyber-attacks. As a result, it was confirmed that the accuracy of judgment against simulated attack test data could be improved to about 88% without lowering the accuracy of judgment against the original test data. In addition, when analyzing the test data of the deception attack that went undetected, it was discovered that it was possible to deal with a simple rule such as judging a combination of specific operations as a deception attack, which made it possible to prevent virtually all deception attacks.
Future Plans
In the future, Fujitsu plans to expand the application of this technology not only to counter cyber-attacks, but also to a variety of other areas to improve the security of systems using AI. In fiscal 2021, Fujitsu additionally aims to commercialize these techniques as part of a security enhancement technology offering.
(1) AI model AI technology that automatically determines whether action needs to be taken in response to a cyberattack. https://bit.ly/31QacSk
(2) Ensemble learning Refers to techniques that improve accuracy by combining results from multiple AI models
About Fujitsu
Fujitsu is the leading Japanese information and communication technology (ICT) company offering a full range of technology products, solutions and services. Approximately 130,000 Fujitsu people support customers in more than 100 countries. We use our experience and the power of ICT to shape the future of society with our customers. Fujitsu Limited (TSE:6702) reported consolidated revenues of 3.9 trillion yen (US$35 billion) for the fiscal year ended March 31, 2020. For more information, please see www.fujitsu.com.
About Fujitsu Laboratories
Founded in 1968 as a wholly owned subsidiary of Fujitsu Limited, Fujitsu Laboratories Ltd. is one of the premier research centers in the world. With a global network of laboratories in Japan, China, the United States and Europe, the organization conducts a wide range of basic and applied research in the areas of Next-generation Services, Computer Servers, Networks, Electronic Devices and Advanced Materials. For more information, please see: http://www.fujitsu.com/jp/group/labs/en/.
Fujitsu Laboratories Ltd.
Security Laboratory
E-mail: aicysec-inquiry@ml.labs.fujitsu.com
Source: Fujitsu Ltd
Sectors: CyberSecurity, Artificial Intel [AI]
Copyright ©2026 JCN Newswire. All rights reserved. A division of Japan Corporate News Network. |
Latest Release

Application Submitted for LENVIMA(R) (lenvatinib) in Japan Seeking Approval of Additional Dosage and Administration for Combination with WELIREG(R) (belzutifan) for Renal Cell Carcinoma that has Progressed After Chemotherapy
Mar 27, 2026 20:14 JST
| 
Hitachi and MUFG Bank expand NextGen model to finance vehicles and charging infrastructure for decarbonized mobility
Mar 27, 2026 19:44 JST
| 
Eisai and Nuvation Bio Announce Marketing Authorisation Application for Taletrectinib for the Treatment of Advanced ROS1-Positive Non-Small Cell Lung Cancer Validated by the European Medicines Agency
Mar 27, 2026 18:19 JST
| 
New "L00 Series" Train for the Seibu Railway's Yamaguchi Line Begins Commercial Operation
Mar 27, 2026 16:51 JST
| 
Fujitsu develops high-sensitivity, high-resolution infrared sensor to expand monitoring capabilities in defense and disaster prevention
Mar 27, 2026 14:07 JST
| 
Sharp Develops Long-Range Video Monitoring Technology
Mar 26, 2026 22:39 JST
| 
OKI and Hitachi Agree to Integrate Businesses Related to Automated Teller Machines (ATMs) and Other Automated Equipment
Mar 26, 2026 22:10 JST
| 
Hitachi Rail to manufacture rolling stock for Seibu Railway"s new Fine Dining Train
Mar 26, 2026 15:13 JST
| 
Royal Healthcare in Singapore provides NEC's "FonesVisuas Test" for Disease Risk Prediction
Mar 26, 2026 11:21 JST
| 
MHI-AP Awarded Boiler Retrofit Contract for Waste-to-Energy Facility in Singapore
Mar 26, 2026 11:07 JST
| 
Sumitomo Heavy Industries and NEC to develop system capable of identifying and reporting near-miss incidents
Mar 25, 2026 14:27 JST
| 
NEC Orchestrating Future Fund Invests in U.S.-based AGI7, Provider of "Alpha Vision" Platform for Autonomous Operations of AI Agents in Physical Spaces
Mar 25, 2026 13:17 JST
| 
Fujitsu and The University of Osaka develop new technologies for chemical material energy calculations on early-FTQC quantum computers
Mar 25, 2026 10:58 JST
| 
HIES introduces plant-based lubricant that reduces air compressor lifecycle CO(2) emissions by 40%
Mar 24, 2026 18:07 JST
| 
Fujitsu and Umios conduct joint pilot project for electronic traceability system to visualize seafood distribution
Mar 24, 2026 14:01 JST
| 
Fujitsu-developed traffic simulation system utilized in Maebashi City's public transportation planning
Mar 23, 2026 14:24 JST
| 
Hitachi Receives the 2026 Catalyst Award, a Global Recognition for Building an Inclusive Organization
Mar 23, 2026 11:49 JST
| 
Results from Real-World, Long-Term Treatment Persistence with LEQEMBI(R) (lecanemab-irmb) in the United States Presented at AD/PD(TM) 2026
Mar 23, 2026 11:19 JST
| 
Honda to Expand Motorcycle Production Capacity in India by Adding New Motorcycle Production Line to its Second Plant
Mar 19, 2026 18:32 JST
| 
Honda WN7 Electric Motorcycle Wins Gold Award at iF DESIGN AWARD 2026
Mar 19, 2026 18:16 JST
|
More Latest Release >>
|